

Configure Kerberos authentication based on FreeIPA via ADCM
Overview
To kerberize a cluster using FreeIPA, follow the steps below:
-
In ADCM web UI, go to the Clusters page. Select an installed and prepared ADPS cluster, and run the Manage Kerberos action.
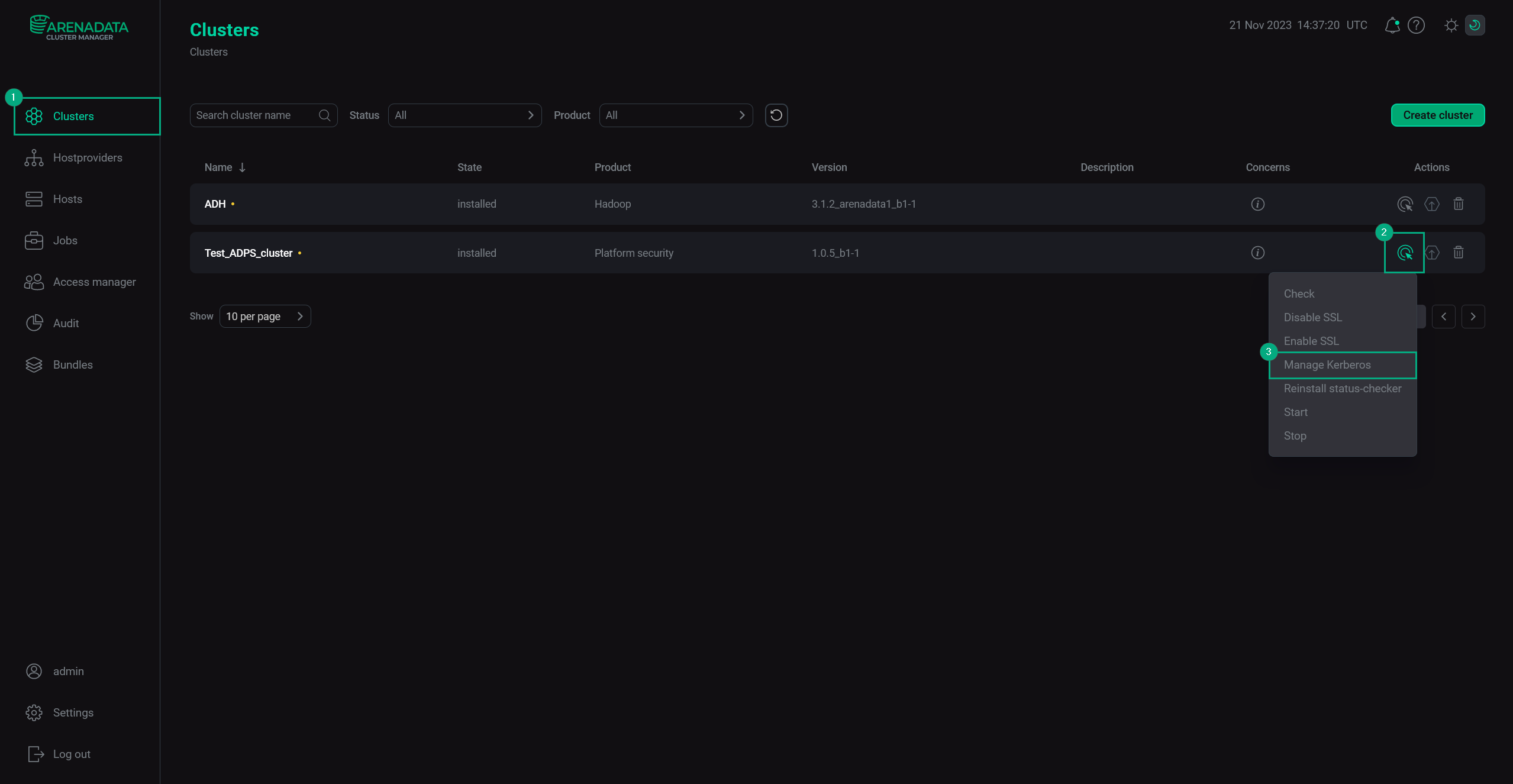 Manage Kerberos
Manage Kerberos -
In the pop-up window, turn on the Existing FreeIPA option.
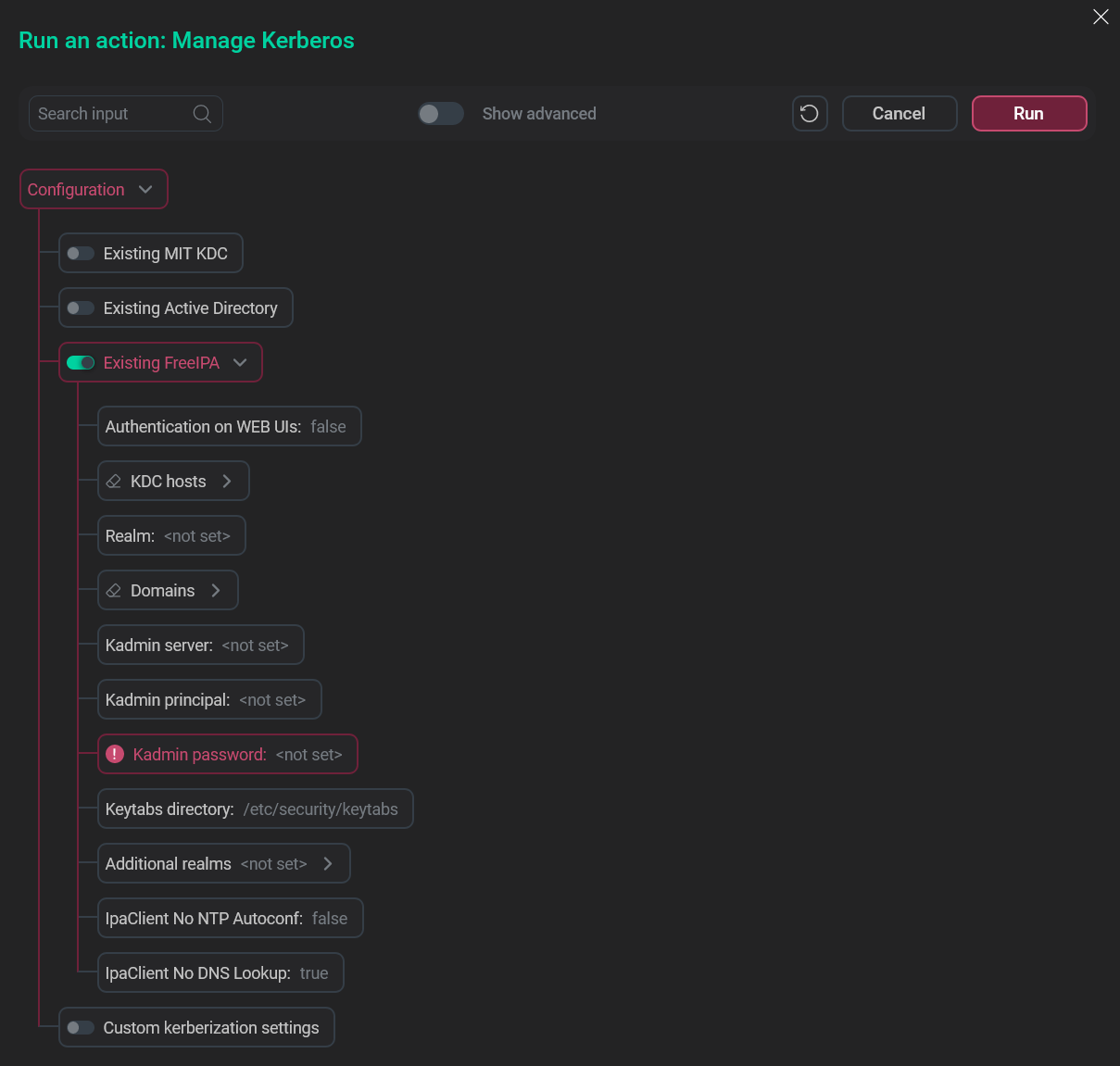 Choose the relevant option
Choose the relevant option -
Fill in the FreeIPA Kerberos parameters.
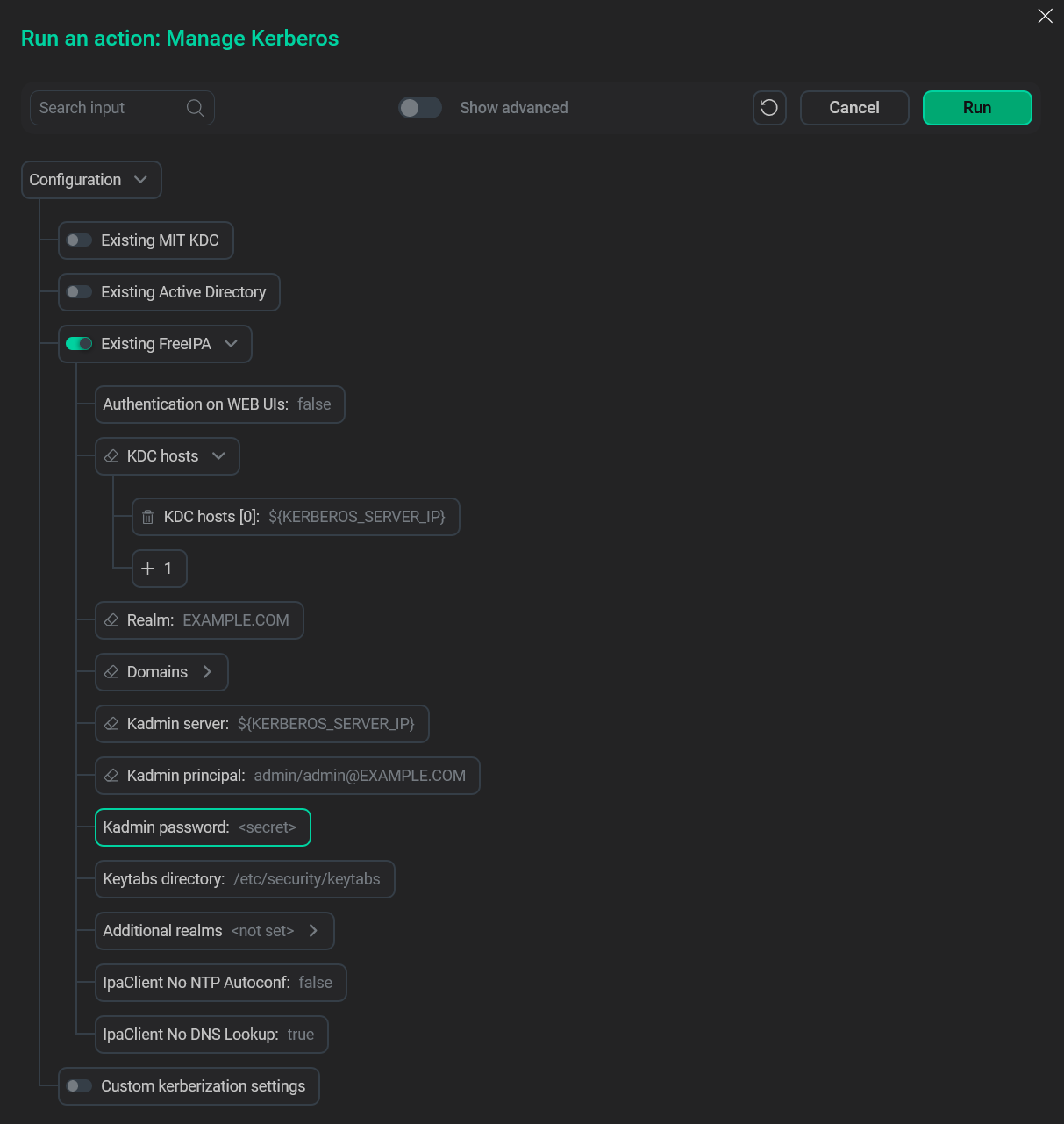 FreeIPA Kerberos fields
FreeIPA Kerberos fields -
Click Run, wait for the job to complete and proceed to setting up Kerberos in the cluster.
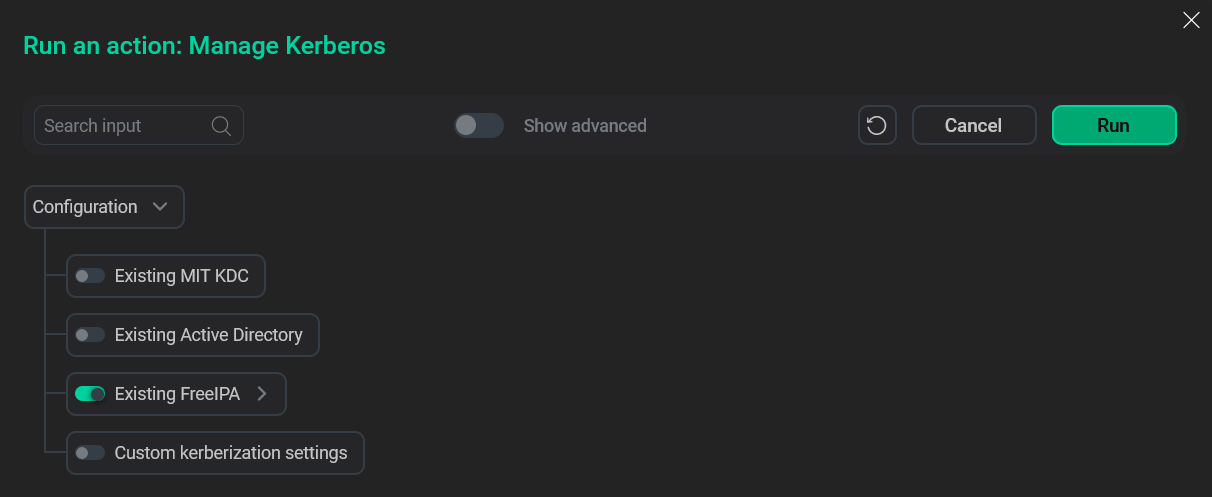 Run the action
Run the action
FreeIPA Kerberos parameters
The following parameters are required to kerberize your ADPS cluster with FreeIPA.
You can get values for these by running ipa user-find <ipa_admin> on your FreeIPA server, where <ipa_admin> is your IPA Admin user.
| Parameter | Description |
|---|---|
Authentication on WEB UIs |
Enables Kerberos authentication on Web UIs |
KDC hosts |
One or more KDC hosts with running FreeIPA server(s). Only FQDN is acceptable |
Realm |
Kerberos realm to connect to the FreeIPA server |
Domains |
One or more domains associated with FreeIPA |
Kadmin server |
Host where |
Kadmin principal |
Principal name used to connect via |
Kadmin password |
IPA Admin password |
Keytabs directory |
Directory of the keytab file that contains one or several principals along with their keys |
Additional realms |
Additional Kerberos realms |
IpaClient No NTP Autoconf |
Disables the NTP configuration during the IPA client installation |
IpaClient No DNS Lookup |
Disables the DNS lookup for FreeIPA server during the IPA client installation |